Security teams and IT operations often work in silos and do not collaborate on cyber defense. The lack of cohesion between the two departments leads to inept security measures that increase the risk of cyberattacks.
As a solution, companies are increasingly relying on SecOps to improve the team’s collective ability to detect, prevent, and mitigate threats across the software lifecycle.
This article explains the value of the SecOps culture in agile and DevOps teams. Continue reading to learn how SecOps bridges security gaps and gets application safety up to speed with the pace of modern software development.
What is SecOps?
SecOps is a set of practices that automate crucial security tasks and ensure close collaboration between security and operations teams. This methodology creates a shared security platform that breaks down barriers between departments, reduces risk, and improves overall agility.
In a SecOps culture, security measures occur across the software lifecycle and are not a “final check” before a product release. Setting up SecOps leads to:
- More robust overall cybersecurity.
- Fewer configuration errors.
- Quick and effective incident responses.
- More reliable compliance policies.
- Fewer data breaches.
- Better communication between different development, operations, and security teams.
Like DevOps, SecOps is a response to the challenges and risks of having dysfunctional teams. Using SecOps to bring security and IT operations together enables a business to:
- Automate tests and processes to speed up and make security measures more reliable.
- Increase employee accountability.
- Ensure better visibility into development, testing, and production environments.
- Set up remediation measures at every stage of the software development lifecycle (SDLC).
The rise of SecOps is in part a result of the popularity of cost-effective cloud solutions. Cloud deployments add speed and agility to development, forcing teams to find ways to ensure security models keep up with rapid workflows.
Learn how to transition to DevOps in 6 simple steps and gain an edge over companies still relying on traditional software development.
What Are the Goals of SecOps?
The primary goal of SecOps is to improve the security posture of a business and its products. Secondary objectives are:
- Reframe application security as a shared responsibility between all teams.
- Raise security awareness across the company.
- Simplify and standardize security operations.
- Create increased transparency across all departments and environments.
According to Gartner’s research, companies are aware of 99% of exploited security flaws at the time of the breach. Another vital objective of SecOps is to ensure the team patches every known vulnerability before a hacker has enough time to launch an attack.
Due to similar goals and some overlap, SecOps is often confused with DevSecOps (DevOps Security). However, there is a difference between the two methodologies. DevSecOps integrates security into the development cycle. Besides integrating security, SecOps also maintains protection and compliance for applications, underlying systems, and data.
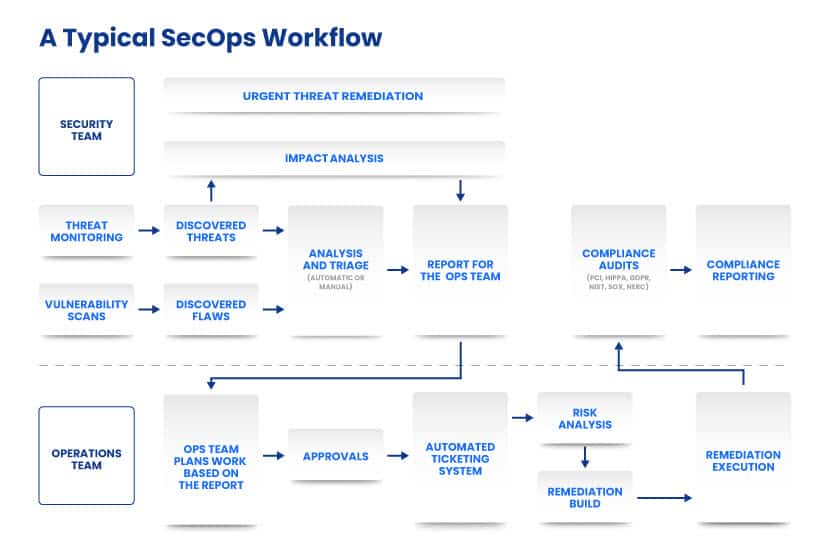
What Does the SecOps Team Do?
A well-rounded SecOps team has clear roles and responsibilities. The staff is in charge of setting up and managing:
- Threat detection.
- Incident response.
- Notification and alerting.
- Security orchestration.
While the SecOps operators interact with other departments, this team is typically self-contained and often composes of a mix of in-house and outsourced staff. Critical roles for every SecOps team are:
- SOC manager: A manager oversees the entire SecOps operation. Besides managing the team, this person also communicates with business leaders to ensure the company understands the SecOps initiative.
- Incident responder: These staff members are in charge of identifying threats and prioritizing flaws. A responder also configures security tools for optimal protection.
- Security investigator: An investigator identifies affected devices and performs in-depth threat analysis. This staff member also determines mitigation strategies.
- Advanced security analyst: This team member looks for unknown threats, analyzes past breach attempts, and suggests improvements (new tools, products, protocols, etc.).
- Security engineer: An engineer manages the overall security architecture and ensures compliance with legal rules. Another common name for an engineer is a security architect.
Depending on the company’s needs, a SecOps unit can also have additional roles. Businesses often employ cloud security experts, digital ethics professionals, compliance auditors, and third-party risk specialists to boost protection across all verticals.

SecOps SOCs (Security Operations Centers)
A SecOps team operates out of a security operations center (SOC). A SOC typically runs 24/7 as the staff works in shifts to log activity and monitor for threats. There are four primary SOC models:
- A virtual SOC that runs in an online environment.
- A multifunction SOC in which SecOps operators share a physical space with other internal teams.
- A hybrid SOC with in-house and third-party staff working in a facility, virtual space, or a mix of both.
- A dedicated SOC that allows the in-house SecOps department to isolate and work from a committed physical space.
Regardless of the model, the technical capabilities of a SOC are always the same.
What Are the Benefits of SecOps?
Investing in SecOps offers a range of benefits that are nearly impossible to achieve when security and operations teams work in silos.

Robust Cybersecurity
SecOps adds security controls to all major workflows and requires multiple teams to take part in cyber protection. As a result, a company with SecOps is less likely to fall victim to a cyberattack.
The SOC’s 24/7 work hours also help protect digital assets. Continuous monitoring is crucial to discovering initial signs of malicious activity. Around-the-clock supervision also means code is more secure when it reaches the production environment.
With security processes built into the development cycle, the team is also able to:
- Patch faster and more often.
- Ship safer and more stable code.
- Decrease the number of problem reports.
- Minimize downtime.
Additionally, SecOps helps the security team improve response rates. SecOps operations are also vital to improving the security of cloud platforms.
Better Team Productivity
The team becomes more productive with SecOps due to a lack of distractions. Staff benefits from:
- Automated processes for threat detection.
- Precise alerting with fewer false positives.
- Collaboration with other teams.
- Clearer reporting.
Thanks to a more streamlined approach to cyber protection, the security team can focus on worthwhile threats. Also, SecOps prevents multiple groups of people from duplicating efforts by working on the same alert or incident.
Fewer Compliance Issues
A misconfiguration in infrastructure or application can lead to severe compliance issues. The risk is especially high for businesses that fall under strict regulations, such as GDPR, PCI, or HIPPA.
SecOps practices increase accountability and visibility for compliance risks. Well-configured tools and policies also help meet legal expectations that demand specific monitoring functions and mechanisms.
Our comparison of CCPA and GDPR explains similarities and differences between the two data privacy laws.
Cost-Savings Across the Board
SecOps has one of the highest ROI metrics in the cybersecurity industry. Automation and shared responsibilities save money by:
- Reducing the need for staffing an ever-growing security team.
- Ensuring optimal usage of cloud storage and services.
- Limiting downtime and business disruptions.
- Minimizing the time an attacker can spend within a compromised network.
- Reducing the impact of successful breaches (the cost of data loss, lawsuits, reputation damage, etc.).
Read about cybersecurity best practices that improve security regardless of whether you have a dedicated SecOps team.
What are the Challenges of SecOps?
While SecOps offers significant advantages, the methodology can be challenging to put into practice. Below are the three main challenges of implementing SecOps.
Talent Shortage
Finding the right staff is one of the biggest challenges for SecOps implementation. The talent pool is shallow due to skill shortages as a successful SOC requires highly experienced personnel.
An inexperienced team can struggle with tight deadlines for security monitoring, testing, and analysis. As expectations change, it can also be difficult for the security team to keep up with the pace of the Ops department.
If you cannot assemble an effective SecOps department, consider outsourcing a SOC team. You can also rely on a mix of in-house and third-party staff so that full-time employees learn from experts.
Resistance to Change
Setting up a SecOps operation requires significant changes to tasks and responsibilities. The change demands the programmers to learn new skill sets and master agile processes. The push for speed may lead to security concerns, resulting in releases of vulnerable code.
Some teams can experience problems when transitioning to SecOps principles. To tackle this challenge, consider doing the following:
- Devote time to training.
- Promote the value of skill-sharing.
- Clarify how processes and tools impact productivity and functionality.
- Try to overlap tools and methods between different teams and departments.
Ensure that the company undergoes a cultural and not a simple process change.
Large Amounts of Data
The scale of data a SecOps team must analyze can be overwhelming. Adopting new practices often leads to alert fatigue among operators. Also, data formats between different departments don’t always align, making analysis even harder.
To help the team handle high amounts of SecOps info, centralize all log data and system alerts. A SIEM solution can correlate, filter, and consolidate data. Security staff should also automate these programs to respond to low-level warnings.
Read about the best SIEM tools DevOps teams rely on to streamline operations in 2021.
Best Practices for Implementing SecOps in Your Organization
Below are five best practices to consider when incorporating SecOps into development workflows.

Regular SecOps Training
The SOC must keep up with the latest SecOps trends to remain effective. Organize a rich training program that includes:
- Regular in-house training sessions.
- Courses that introduce new resources and frameworks.
- Third-party training classes.
Be strategic when creating a training schedule. In-house sessions are cheap and easy to organize, but third-party courses help with radical shifts in tooling or processes.
Make Full Use of SecOps Tools
Tools play a vital role during the SecOps transition. Common tool types that help a team set up and master SecOps include:
- Security monitoring tools that offer visibility over IT systems, identify intrusions, and insider threats.
- Incident response tools that respond to threats through automatic quarantining.
- Testing tools that check code integrity along the DevOps pipeline.
- Configuration management tools that set up test environments and update systems in case of a vulnerability.
- Security automation tools that remove manual tasks and streamline processes.
- Container tools that simplify software delivery, automate developer tasks, and speed up deployments of new features.
Read about automated security testing to learn how the pros optimize and speed up software checks.
Rely on Automation
Companies should try to automate as many operations as possible. Use automation to:
- Streamline testing.
- Detect potential threats.
- Assign risk scores.
- Speed up analysis.
- Run incident responses and threat mitigation.
Automation frees up humans from tedious manual tasks. Teams can focus more on SecOps strategies instead of wasting time on repetitive assignments.
Do Not Overlook Cloud Security
Ensuring security in the cloud is different than protecting traditional systems. Cloud setups are prone to vulnerabilities a less experienced team can overlook.
A SOC must adapt both tools and strategies to protect cloud assets adequately. Good practices include:
- Carefully selecting cloud providers.
- Using less privileged accounts for specific tasks in the cloud.
- Setting up multi-factor authentication for all users.
- Enabling write-once storage for logs.
Learn how to create a cloud security policy, a crucial step when protecting on-cloud assets.
Run Red VS. Blue Team Exercises
One of the best activities that keep a SecOps team in good shape are red vs. blue team exercises. In this practice, the department splits up into two groups: the red team that acts as the aggressor, and the blue team sets up defenses.
The attacking side uses different strategies in attempts to breach the system, including:
- Penetration testing.
- Various forms of social engineering.
- Port and vulnerability scanning.
The red team can also use custom tools to discover and exploit security flaws. If attackers make it inside the network, the goal is to escalate privileges and either access sensitive data or sabotage a system.
Meanwhile, the blue team runs standard SecOps activities, such as analyzing threats, identifying breach attempts, and relying on security tools.
Once the exercise ends, both attackers and defenders generate reports on their activity. A SOC manager reviews these reports and looks for opportunities to improve security posture.
What is the Future for SecOps?
SecOps will continue to evolve over the years as new cyber threats emerge, and security teams discover new protection methods. Here are some of the most notable trends you can expect to develop in the coming years:
- AI and machine learning will become a more central part of SecOps. SOCs will use AI to become more automated, customized, and dynamic.
- Companies will dedicate more time to developing success metrics for SOCs. These metrics will help better evaluate and improve performance.
- Threat hunting will become more proactive to stay ahead of attackers.
- Teams will rely more on third-party threat intelligence services.
Learn about DevOps trends in 2021 to ensure your team keeps up with the latest agile practices.
A Reliable Approach to Security Ideal for DevOps Teams
SecOps is a requirement for any company that delivers software at high velocity. Set up a SecOps department to integrate security into the SDLC and ensure your team works without needless setbacks.